Hi,
This project is about our existing gateway designs using nRF SDK for Mesh v5.0.0. The firmware is based on the serial example using a custom machine-machine interface. Only modifications to the serial example were increasing the replay cache to 1024 entries and adding a variation of the Packet Send command at the opcode 0xB0 that allows us to use the Packet Send functionality using unicast addresses directly instead of address handles. This latter detail is important as we use that Packet Send command.
There are three gateways each with a different unicast address. The mesh network consists of three subnets and three appkeys, each gateway being responsible for one subnet and appkey. There are also two provisioners first one starting from 0x0001 and the other from 0x2FFF.
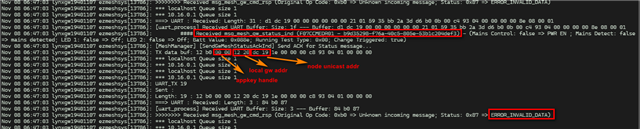
On one gateway with unicast address 0x2012, our Packet Send keeps returning error code 0x87 for ERROR_INVALID_DATA. This is one example:
Nov 14 09:14:34 lynxgw19401107 ezmeshsys[19450]: [MeshManager] [SendGwMeshStatusAckInd] Send ACK for Status message... Nov 14 09:14:34 lynxgw19401107 ezmeshsys[19450]: TX data buf: 12 b0 00 00 12 20 78 01 1e 00 00 00 c8 93 04 01 00 00 00 Nov 14 09:14:34 lynxgw19401107 ezmeshsys[19450]: *** localhost Queue size 1 Nov 14 09:14:34 lynxgw19401107 ezmeshsys[19450]: *** 10.16.0.1 Queue size 1 Nov 14 09:14:34 lynxgw19401107 ezmeshsys[19450]: *** localhost Queue size 1 Nov 14 09:14:34 lynxgw19401107 ezmeshsys[19450]: *** 10.16.0.1 Queue size 1 Nov 14 09:14:34 lynxgw19401107 ezmeshsys[19450]: UART_TX 19 Nov 14 09:14:34 lynxgw19401107 ezmeshsys[19450]: Sent : Nov 14 09:14:34 lynxgw19401107 ezmeshsys[19450]: Length: 19 : 12 b0 00 00 12 20 78 01 1e 00 00 00 c8 93 04 01 00 00 00 Nov 14 09:14:34 lynxgw19401107 ezmeshsys[19450]: ===> UART : Received: Length: 3 : 84 b0 87 Nov 14 09:14:34 lynxgw19401107 ezmeshsys[19450]: [uart_process] Received UART Buffer: Size: 3 --- Buffer: 84 b0 87 Nov 14 09:14:34 lynxgw19401107 ezmeshsys[19450]: >>>>>>>> Received msg_mesh_gw_cmd_rsp (Original Op Code: 0xb0 => Unknown incoming message; Status: 0x87 => ERROR_INVALID_DATA)
Our gateway is trying to send a simple ACK message in reply to a device with unicast address 0x0178 but as you can see, no luck. This image may be clearer:
In serial_handler_mesh.c, there are two places in our code that can return ERROR_INVALID_DATA, lines 31 and 57:
/*
Send a packet direct to a unicast address
Do not use for a group address
*/
static void handle_cmd_direct_packet(const serial_packet_t * p_cmd)
{
nrf_mesh_tx_params_t tx_params;
memset(&tx_params, 0, sizeof(tx_params));
serial_evt_cmd_rsp_data_packet_send_t rsp;
rsp.token = nrf_mesh_unique_token_get();
uint32_t status;
nrf_mesh_address_t address;
memset(&address, 0, sizeof(address));
// Address handle is actually the 16 bit unicast address here
address.value = p_cmd->payload.cmd.mesh.packet_send.dst_addr_handle;
address.type = NRF_MESH_ADDRESS_TYPE_UNICAST;
address.p_virtual_uuid = NULL;
tx_params.dst = address;
dsm_local_unicast_address_t valid_src_addrs;
dsm_local_unicast_addresses_get(&valid_src_addrs);
if (p_cmd->payload.cmd.mesh.packet_send.src_addr < valid_src_addrs.address_start ||
p_cmd->payload.cmd.mesh.packet_send.src_addr >= valid_src_addrs.address_start + valid_src_addrs.count)
{
status = NRF_ERROR_INVALID_ADDR;
} else
{
{
status = dsm_tx_secmat_get(DSM_HANDLE_INVALID,
p_cmd->payload.cmd.mesh.packet_send.appkey_handle,
&tx_params.security_material);
}
if (status == NRF_SUCCESS)
{
tx_params.src = p_cmd->payload.cmd.mesh.packet_send.src_addr;
tx_params.ttl = p_cmd->payload.cmd.mesh.packet_send.ttl;
tx_params.force_segmented = p_cmd->payload.cmd.mesh.packet_send.force_segmented;
tx_params.transmic_size = (nrf_mesh_transmic_size_t) p_cmd->payload.cmd.mesh.packet_send.transmic_size;
if (p_cmd->length > NRF_MESH_SERIAL_PACKET_OVERHEAD + SERIAL_CMD_MESH_PACKET_SEND_OVERHEAD)
{
tx_params.p_data = p_cmd->payload.cmd.mesh.packet_send.data;
tx_params.data_len = p_cmd->length - SERIAL_CMD_MESH_PACKET_SEND_OVERHEAD - NRF_MESH_SERIAL_PACKET_OVERHEAD;
}
else
{
tx_params.p_data = NULL;
tx_params.data_len = 0;
}
tx_params.tx_token = rsp.token;
status = nrf_mesh_packet_send(&tx_params, NULL);
}
}
serial_handler_common_cmd_rsp_nodata_on_error(p_cmd->opcode, status, (uint8_t *) &rsp, sizeof(rsp));
}
However I'm not sure which one it is. The device is currently onsite with no remote debug access. Could you perhaps point me to the issue?
Regards,
Arif
