Hi,
I am using SDK v2.6.1.
Is there any course available on DevAcademy for WebSockets?
For WebSocket i take reference of v2.6.1/zephyr/samples/net/sockets/websocket_client,
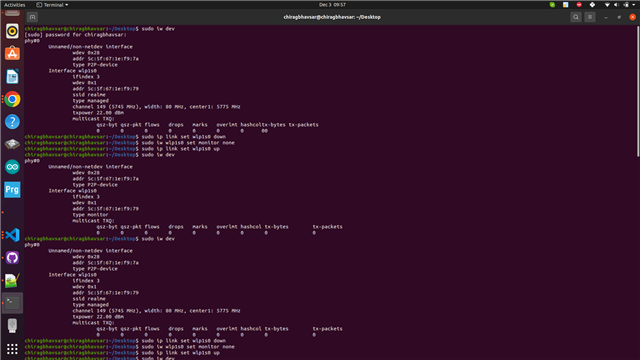
when i try to give wifi credential using wifi connect -s <ssid> -k 1 -p <password> then i have got wifi: command not found so require to give wifi credential?or how we are able to see WebSocket reference code output,
I need an example that merges WebSocket and HTTPS. Could you also provide feedback on how to merge both into a single code?