Suddenly DFU OTA fails most of the time while trying to update units with code & "not secure" bootloader that has been working for years. The FW upload stops at 2% to 8% but if i restart my phone sometimes it reaches 15% and on happy days I can update the unit after rebooting the phone.
With the same DFU app DFU update works well with another unit with "secure" bootloader.
I am NOT trying to update a unit with "not secure" bootloader with code made for units with "secure bootloader" and vice versa.
What can suddenly be the problem?
Phone: Samsung Galaxy S21 Ultra 5G
Android version: 14
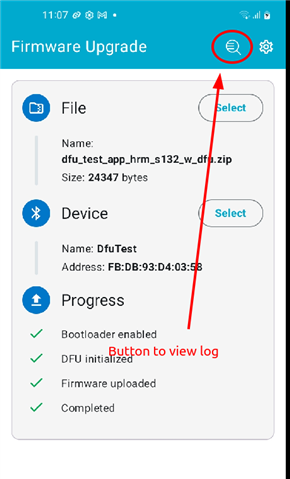
DFU app version: 2.9.0 (build 24123065)