I use the nRF52840 dongle on Windows to sniff BLE using the Wireshark extcap. I have been using the python extcap, but recently installed the new executable extcap. I noticed that the Channel Selection Algorithm (CSA) is always set to 0 (false) using the new extcap for a given device (Tile tracker). I reverted to to the old python excap and confirmed that the same device shows in Wireshark as 1 (true), meaning that the device is using CSA #2. I confirmed with two other tools that the device is actually using CSA #2. The CRC shows as correct when using both extcaps. I asked an AI to calculate CRC and was told that the new excap (executable) was wrong. I asked the AI to calculate the CRC assuming that the CSA bit was set to true, and it calculated the same CRC as was sent over the air.
From this, it seems that the new executable extcap for BLE sniffing is correctly receiving the data and calculating the CRC correctly. However, it is passing the wrong value for CSA to Wireshark.
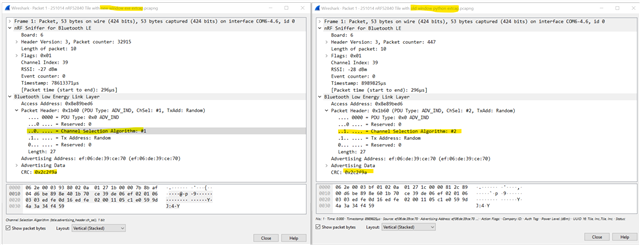
Below is advertising from the same Tile at roughly the same time, so that the payload is identical. The new extcap on the left has CSA set to 0. The old extcap on the right has CSA set to 1. The CRC is the same for both collections.
I'm not asking for help so much as submitting a bug.


