I have observed a Softdevice assertion, built from the v3.1.0 commit. https://github.com/nrfconnect/sdk-nrfxlib/tree/v3.1.0
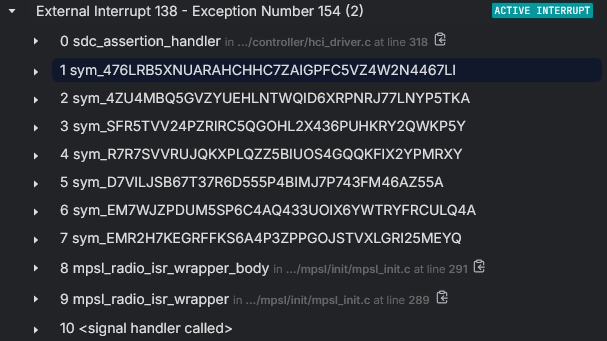
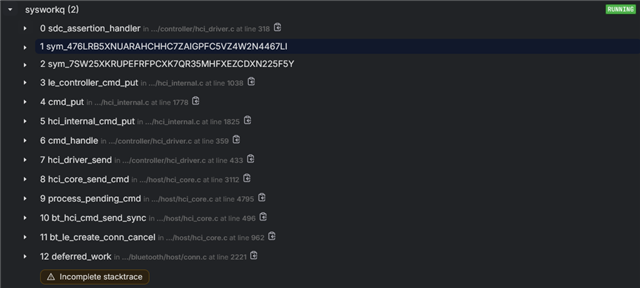
The assertion was seen through Memfault, I believe the `file` and `line` parameters have been overwritten, but I have the backtrace through the obfuscated symbols.