Hi everyone,
I’ve been following the AWS IoT sample, but so far I haven’t been able to establish a connection.
We’re running on a custom board using the nRF54L15, connected to a Quectel EG915 modem via UART. We have a thread managing the PPP connection: it brings the interface up (net_if_up()) and waits for the L4 connection events. Once the connection is established, we perform an SNTP sync using the IPv4 address resolved with zsock_getaddrinfo(). After the time sync completes, a callback notifies the AWS IoT MQTT worker to start the MQTT connection.
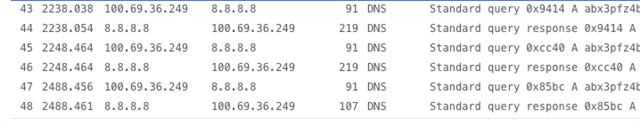
Issue 1: DNS Resolution for the AWS IoT Broker
DNS resolution for the broker fails unless we force a static IP.
This is the logic:
if (sizeof(CONFIG_MQTT_HELPER_STATIC_IP_ADDRESS) > 1) {
conn_params->hostname.ptr = CONFIG_MQTT_HELPER_STATIC_IP_ADDRESS;
LOG_DBG("Using static IP address: %s", CONFIG_MQTT_HELPER_STATIC_IP_ADDRESS);
} else {
LOG_DBG("Resolving IP address for %s", conn_params->hostname.ptr);
}
err = zsock_getaddrinfo(conn_params->hostname.ptr, NULL, &hints, &result);
if (err) {
LOG_ERR("getaddrinfo() failed, error %d", err);
return -err;
}
zsock_getaddrinfo() returns -3, which is strange because the same function works fine for resolving the NTP server.
Even more confusing: on the SIM card portal, we can see the DNS query for the AWS broker happening correctly — yet our code still times out.
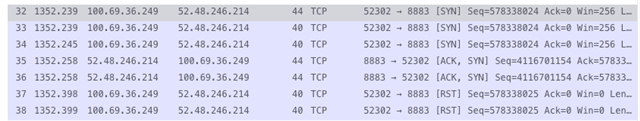
To move forward, we tried defining CONFIG_MQTT_HELPER_STATIC_IP_ADDRESS with the IPv4 address, but we still cannot connect.
The connection returns -116 (timeout). Initially we suspected a certificate issue, but again, from the SIM portal we can see a response coming back from the server — but since it’s TLS, we can’t decode it.
Has anyone experienced this? Could it be related to the PPP setup?
I've attached the key parts of my prj.conf below.
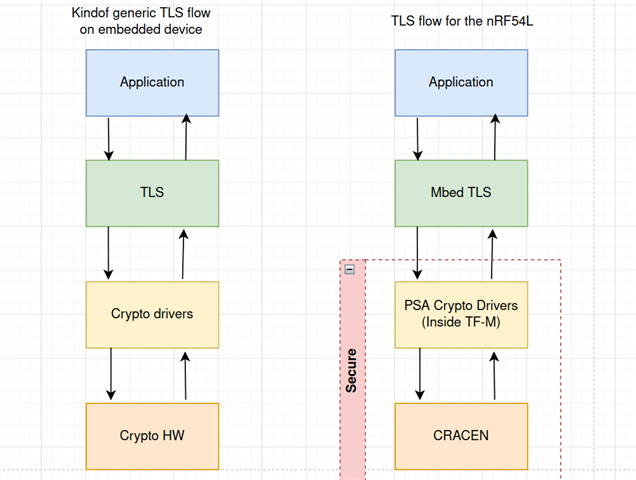
Issue 2: Handling Certificates in Production
What is the recommended way to manage certificates securely on the nRF54L15?
We’ve looked at the TF-M examples, but we’re still unsure how this should work in a real production workflow.
Key questions:
-
How should certificates be provisioned on a production device?
-
Can they be embedded in the firmware image and then stored securely by TF-M at runtime?
-
Should they be erased from normal flash afterwards?
-
What’s the typical workflow for securely flashing these assets when manufacturing devices?
Any insight from someone who has already implemented this would be extremely helpful.
# CONFIG_SENSOR=y CONFIG_I2C=y CONFIG_GPIO=y CONFIG_GPIO_PCA953X=y CONFIG_COUNTER=y CONFIG_COUNTER_MICROCHIP_MCP7940N=y CONFIG_NFCT_PINS_AS_GPIOS=y CONFIG_RTC=y CONFIG_LOG=y CONFIG_USE_SEGGER_RTT=y CONFIG_CONSOLE=y CONFIG_RTT_CONSOLE=y CONFIG_UART_CONSOLE=n CONFIG_SERIAL=y CONFIG_UART_INTERRUPT_DRIVEN=y CONFIG_ADC=y CONFIG_NRFX_SAADC=y CONFIG_NRFX_GPPI=y CONFIG_NRFX_TIMER22=y CONFIG_BT=y CONFIG_BT_DEVICE_NAME="smart" # CONFIG_BT_CTLR_TX_PWR_0=y # CONFIG_BT_CTLR_TX_PWR_PLUS_3=y CONFIG_BT_CTLR_TX_PWR_PLUS_4=y # CONFIG_BT_CTLR_TX_PWR_MINUS_40=y # FOTA over Bluetooth # CONFIG_BT_PERIPHERAL=y CONFIG_BOOTLOADER_MCUBOOT=y # CONFIG_BT_SMP=y # CONFIG_MCUMGR=y # CONFIG_NET_BUF=y # CONFIG_ZCBOR=y # CONFIG_MCUMGR_TRANSPORT_BT=y # CONFIG_MCUMGR_TRANSPORT_BT_CONN_PARAM_CONTROL=y # CONFIG_MCUMGR_GRP_IMG=y # CONFIG_MCUMGR_GRP_OS=y # CONFIG_MCUMGR_GRP_OS_BOOTLOADER_INFO=y # CONFIG_MCUMGR_TRANSPORT_BT_REASSEMBLY=y # CONFIG_MCUMGR_TRANSPORT_BT_PERM_RW_AUTHEN=y CONFIG_PWM=y CONFIG_CLOCK_CONTROL=y # CONFIG_SPI=y CONFIG_WDT_LOG_LEVEL_INF=n CONFIG_WATCHDOG=y CONFIG_WDT_DISABLE_AT_BOOT=n CONFIG_REQUIRES_FLOAT_PRINTF=y CONFIG_CRC=y CONFIG_ENTROPY_GENERATOR=y CONFIG_REQUIRES_FULL_LIBC=y CONFIG_JSON_LIBRARY=y CONFIG_TEST_RANDOM_GENERATOR=y CONFIG_INIT_STACKS=y CONFIG_HW_STACK_PROTECTION=y # NVS for persistent storage CONFIG_ZMS=y # Flash for FOTA CONFIG_FLASH=y CONFIG_FLASH_MAP=y CONFIG_STREAM_FLASH=y CONFIG_IMG_MANAGER=y # POSIX CONFIG_POSIX_API=y CONFIG_POSIX_NETWORKING=y CONFIG_ZVFS_OPEN_MAX=21 CONFIG_POSIX_FD_MGMT=n CONFIG_POSIX_MESSAGE_PASSING=n CONFIG_POSIX_THREAD_THREADS_MAX=0 # Networking over PPP CONFIG_NETWORKING=y CONFIG_NET_NATIVE=y CONFIG_NET_L2_PPP=y CONFIG_NET_IPV4=y CONFIG_NET_UDP=y CONFIG_NET_TCP=y CONFIG_NET_SOCKETS=y CONFIG_NET_SOCKETS_SOCKOPT_TLS=y # DNS CONFIG_NET_LOG=y CONFIG_DNS_RESOLVER=y CONFIG_NET_L2_PPP_OPTION_DNS_USE=n CONFIG_DNS_SERVER_IP_ADDRESSES=y CONFIG_DNS_SERVER1="8.8.8.8" CONFIG_DNS_RESOLVER_MAX_SERVERS=1 CONFIG_DNS_RESOLVER_ADDITIONAL_BUF_CTR=2 CONFIG_NET_SOCKETS_DNS_TIMEOUT=5000 CONFIG_DNS_RESOLVER_LOG_LEVEL_DBG=y # SNTP CONFIG_SNTP=y # Network management CONFIG_NET_MGMT=y CONFIG_NET_MGMT_EVENT=y CONFIG_NET_CONNECTION_MANAGER=y CONFIG_NET_CONFIG_SETTINGS=y CONFIG_NET_CONFIG_NEED_IPV4=y CONFIG_NET_DHCPV4=y CONFIG_NET_MAX_CONN=6 CONFIG_NET_SOCKETS_POLL_MAX=8 CONFIG_NET_SOCKETS_OFFLOAD=n CONFIG_NET_CONTEXT_SNDTIMEO=y CONFIG_NET_CONTEXT_RCVTIMEO=y CONFIG_NET_MAX_CONTEXTS=3 # PSA Crypto for SHA-1 (recommended over legacy mbedtls) CONFIG_NRF_SECURITY=y CONFIG_PSA_WANT_ALG_SHA_1=y # AWS IoT Core CONFIG_AWS_IOT=y CONFIG_AWS_IOT_BROKER_HOST_NAME="aaaaaaa.eu-west-1.amazonaws.com" CONFIG_MQTT_HELPER_STATIC_IP_ADDRESS="100.100.100.100" CONFIG_AWS_IOT_CLIENT_ID_STATIC="" # Should be fetched directly in runtime CONFIG_AWS_IOT_CLIENT_ID_MAX_LEN=40 CONFIG_AWS_IOT_TOPIC_UPDATE_DELTA_SUBSCRIBE=y CONFIG_AWS_IOT_TOPIC_GET_ACCEPTED_SUBSCRIBE=y CONFIG_AWS_IOT_TOPIC_GET_REJECTED_SUBSCRIBE=y CONFIG_AWS_IOT_LOG_LEVEL_DBG=y # MQTT helper library CONFIG_MQTT_HELPER=y CONFIG_MQTT_HELPER_SEC_TAG=201 CONFIG_MQTT_HELPER_LAST_WILL=y CONFIG_MQTT_HELPER_LOG_LEVEL_DBG=y CONFIG_MQTT_HELPER_PORT=8883 CONFIG_MQTT_HELPER_PROVISION_CERTIFICATES=n # MQTT - Maximum MQTT keepalive timeout specified by AWS IoT Core CONFIG_MQTT_KEEPALIVE=1200 CONFIG_MQTT_CLEAN_SESSION=y # TLS (provided by nRF Security, not builtin) CONFIG_NRF_SECURITY_ADVANCED=y CONFIG_NORDIC_SECURITY_BACKEND=y CONFIG_MBEDTLS_TLS_LIBRARY=y CONFIG_MBEDTLS_X509_LIBRARY=y CONFIG_NET_SOCKETS_SOCKOPT_TLS=y CONFIG_NET_SOCKETS_TLS_MAX_CONTEXTS=1 CONFIG_MBEDTLS=y CONFIG_MBEDTLS_ENABLE_HEAP=y CONFIG_MBEDTLS_SSL_KEEP_PEER_CERTIFICATE=n CONFIG_MBEDTLS_SSL_SERVER_NAME_INDICATION=y CONFIG_TLS_CREDENTIALS=y CONFIG_TLS_CREDENTIALS_BACKEND_VOLATILE=y CONFIG_MBEDTLS_LOG_LEVEL_DBG=y # CONFIG_BUILD_WITH_TFM=y # CONFIG_TLS_CREDENTIALS_BACKEND_PROTECTED_STORAGE=y # Modem subsystem CONFIG_MODEM=y CONFIG_PM_DEVICE=y CONFIG_MODEM_CELLULAR=y CONFIG_MODEM_CELLULAR_APN="onomondo" # Statistics CONFIG_MODEM_STATS=n CONFIG_SHELL=n # Logging CONFIG_MODEM_MODULES_LOG_LEVEL_DBG=y # NET buffers CONFIG_NET_PKT_TX_COUNT=6 CONFIG_NET_PKT_RX_COUNT=6 CONFIG_NET_BUF_TX_COUNT=12 CONFIG_NET_BUF_RX_COUNT=6 # Modem buffers CONFIG_MODEM_CMUX_MTU=512 CONFIG_MODEM_CMUX_WORK_BUFFER_SIZE=520 # Stack Sizes CONFIG_NET_TX_STACK_SIZE=2048 CONFIG_NET_RX_STACK_SIZE=2048 CONFIG_NET_MGMT_EVENT_STACK_SIZE=1024 ## For workers CONFIG_SYSTEM_WORKQUEUE_STACK_SIZE=4096 CONFIG_ISR_STACK_SIZE=512 CONFIG_MQTT_HELPER_STACK_SIZE=4096 # Heap sizes CONFIG_HEAP_MEM_POOL_IGNORE_MIN=y CONFIG_MBEDTLS_HEAP_SIZE=45000 CONFIG_HEAP_MEM_POOL_SIZE=32000
Best regards,
Fernando Fontes