Hi,
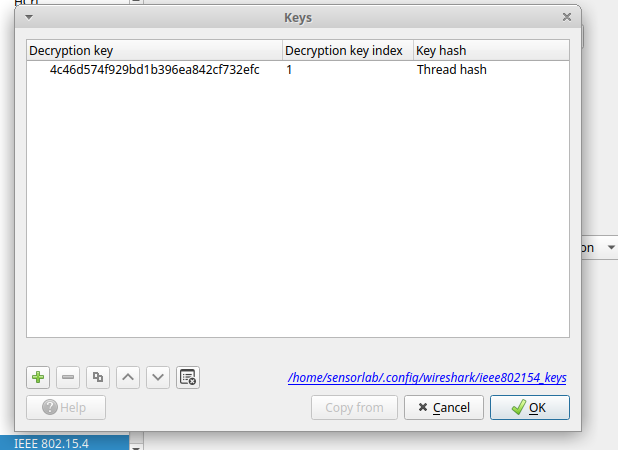
I have developed a Matter-over-Thread light bulb using the Silicon Labs EFR32MG24 platform, with CHIP_CONFIG_SECURITY_TEST_MODE = 1 enabled. In parallel, I have set up an OpenThread Border Router (OTBR) on a Raspberry Pi and retrieved the Thread network key.
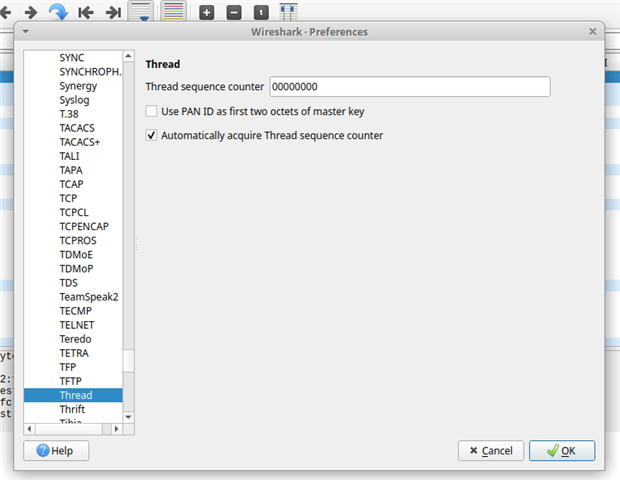
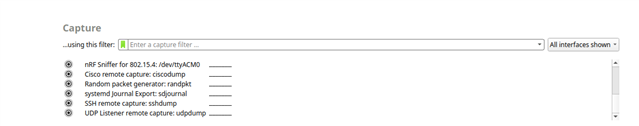
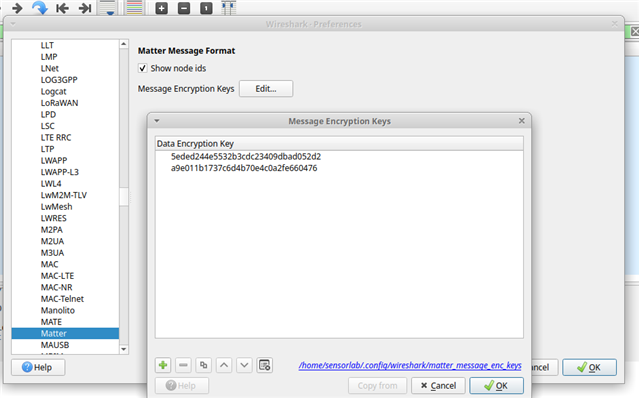
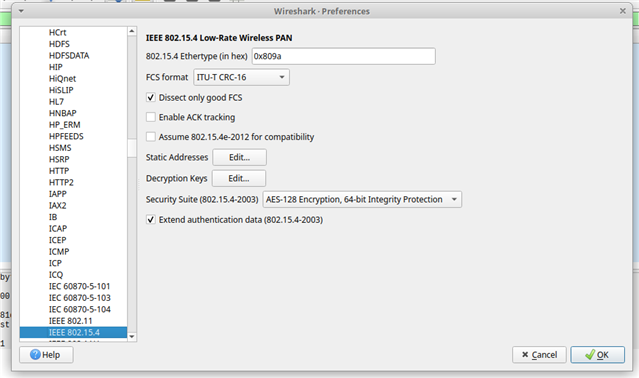
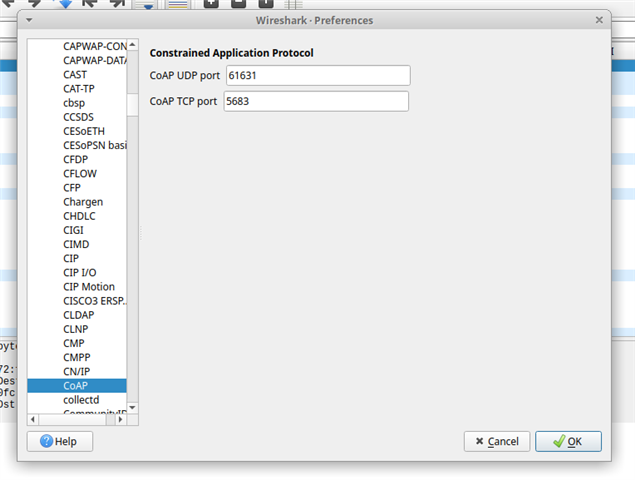
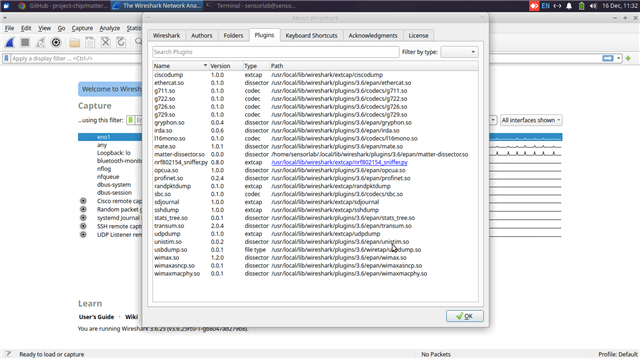
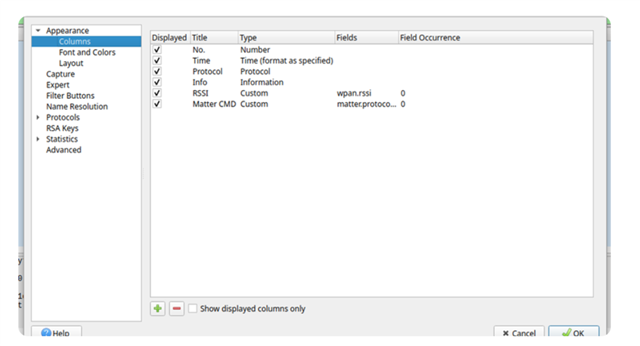
I also built the Matter Wireshark dissector (version 3.6.25) and am using an nRF52840-DK as a Thread sniffer. While I have successfully configured Wireshark for Thread packet decoding and reviewed the reference Matter captures, I am still unable to observe any Interaction Model (IM) traffic in Wireshark. This includes, but is not limited to:
- Command requests and responses
- Attribute read and write operations
- Subscriptions
- Events
- Cluster-level communication
- User Directed Commissioning (UDC)
- On/Off cluster interactions
Despite verifying the Thread configuration and keys, the IM messages are not being decoded or displayed.
For additional context, both the OTBR and chip-tool are built and running in security test mode. I enabled the CHIP_CONFIG_SECURITY_TEST_MODE = 1 flag and built chip-tool using the following command, as specified in config/python/CHIPProjectConfig.h:
gn gen out/debug --args='treat_warnings_as_errors=false'
I have attached screenshots of the Thread keys, Wireshark configuration, and reference captures for your review. I would appreciate your guidance on the correct procedure to capture and decode Matter Interaction Model messages in Wireshark using the nRF52840-DK as Thread Sniffer.
Thank you for your time and support.