I try to write data into the OTP section of the APP core with the following command line:
nrfjprog.exe -f nrf53 --program 'OTP.ihex'
ouput:
[error] [SeggerBackend] - JLinkARM.dll reported error -256 at line 736.
[error] [SeggerBackend] - JLinkARM.dll reported error -256 at line 629.
[error] [SeggerBackend] - JLinkARM.dll reported error -256 at line 3139.
[error] [SeggerBackend] - JLinkARM.dll reported error -256 at line 911.
[error] [SeggerBackend] - JLinkARM.dll reported error -256 at line 3139.
[error] [SeggerBackend] - JLinkARM.dll reported error -256 at line 3139.
[error] [SeggerBackend] - JLinkARM.dll reported error -256 at line 3139.
[error] [SeggerBackend] - JLinkARM.dll reported error -256 at line 3087.
[error] [SeggerBackend] - JLinkARM.dll reported error -256 at line 3112.
[error] [SeggerBackend] - JLinkARM.dll reported error -256 at line 3349.
[error] [SeggerBackend] - JLinkARM.dll reported error -256 at line 3160.
[error] [SeggerBackend] - JLinkARM.dll reported error -256 at line 3176.
[ #################### ] 0.116s | Program file - Done programming
WARNING: A programming operation has been performed without --verify.
WARNING: Programming can fail without error.
If I use Ozone to display the written content in a memory window I can see the data written to the OTP memory. But if I perform a power cycle the OTP section is empty again.
I also tried to use the following command for tests: nrfjprog -f nrf53 --memwr 0x00FF8100 --val 0x7E75
the same problem here: cells are empty after power cycle.
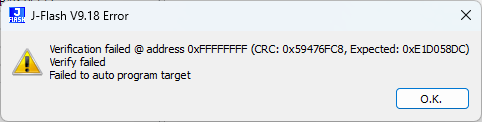
Initially I tried to use JFlash without success. This resulted in an error message even if I enable the OTP bank and disable all others
Any Hints how I can write the OTP section permanently?


