Hello everyone
I am following BLE tutorial on Nordic DevAcademy
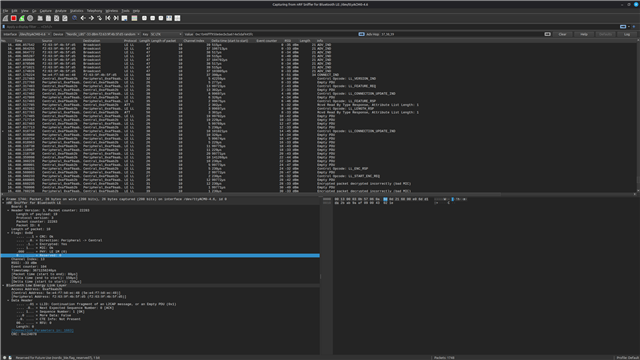
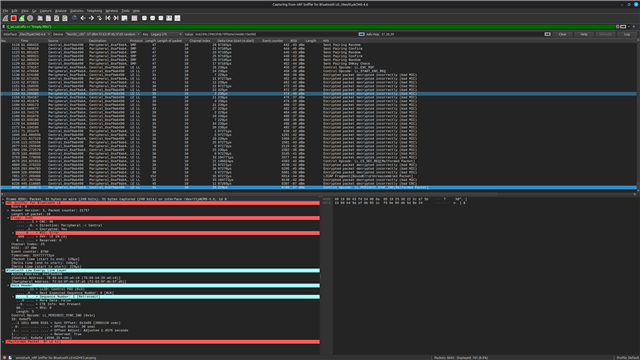
Last part of BLE shows you how to use the nRF52480 to have a BLE sniffer in the Wireshark
I have installed Wireshark and successfully connected and passed all part of training except the very last one.
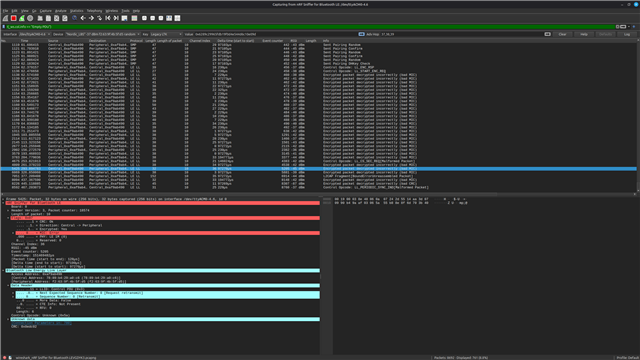
Once devices get bonded and connnected using a SC LTK key the Wireshark does not see any packets from this device anymore
I am using Wireshark v4.6.3 and I have nRF52480 as a dongle. OS is Linux Mint 22.3
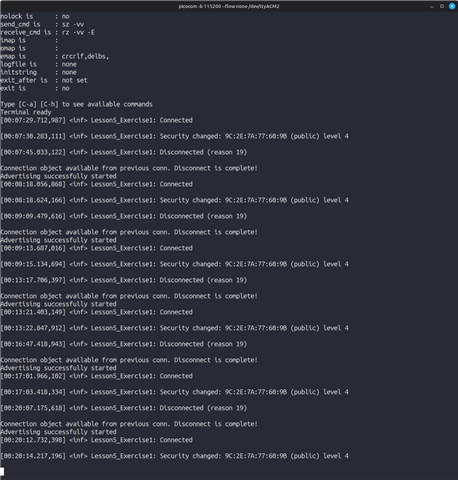
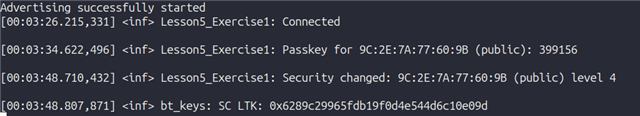
My test board is nRF54l15-DK which has been compiled with the code as in the lesson, I can see the UART output in console as on the image below and I got the SC LTK key and put it into the input box
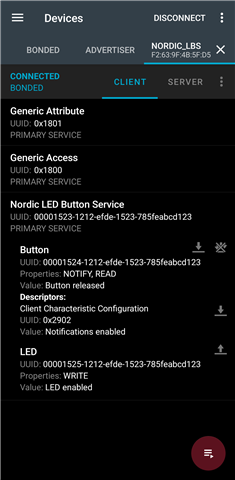
I use Samsung S22 Ultra with nRF Connect application to connect to the nRF54l15-DK and sucessfully do the thing - switch on/off LED and read the status of the button
If I do not use security I see all packets. But once I switch on security and then connect the Wireshark does not receive the packets anymore
As soon as I disconnect from the nRF54l15-DK on my phone in nRF Connect application or if I reset the board I immediately start to receive ADV_IND packets