It looks like the last discussion of Sniffer on Devzone was 2-3 yrs ago.
I’ve ordered the nRF Dongle and will download the Windows-based nRF Sniffer app.
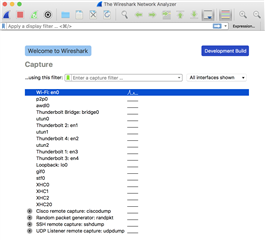
i can run this with WireShark on a Windows VM on my Mac, though I would like a Mac OSX option.
- Any news on that front?
- Any way the Bluetooth hardware built into the MacBook could serve a Mac Sniffer app?
thanks!