Hi all
nrf52840 Development board,sdk is nRF5_SDK_15.2.0_9412b96,PC is windows 10
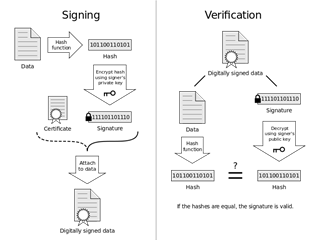
I want to use the DFU to update my file,but I find that only the Init packet is signatured.If the attacker uses the init packet which is signatured and adds his aclicious code,the firmware of ble device will be updated using the aclicious code.Is this a security vulnerablility?