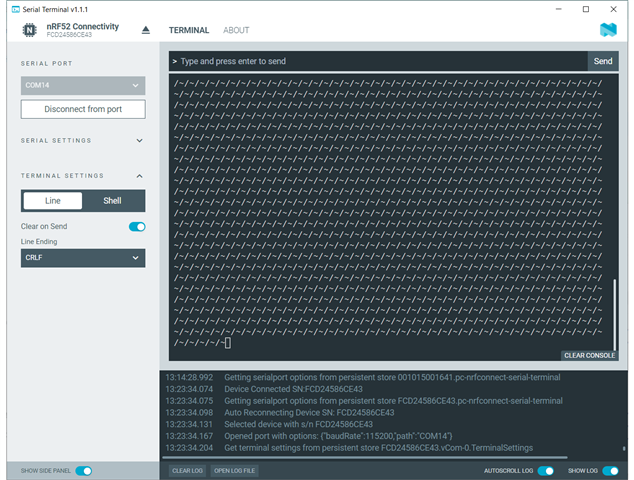
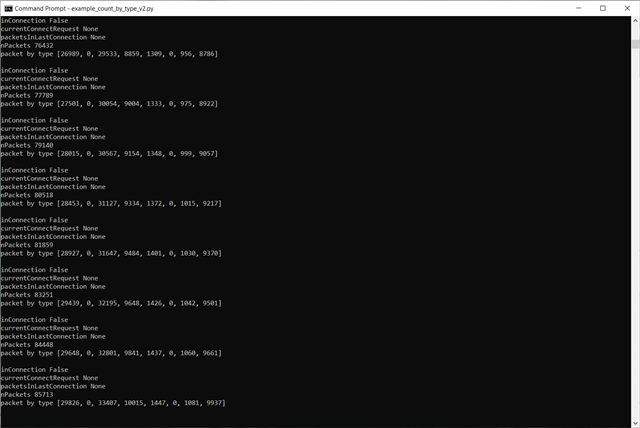
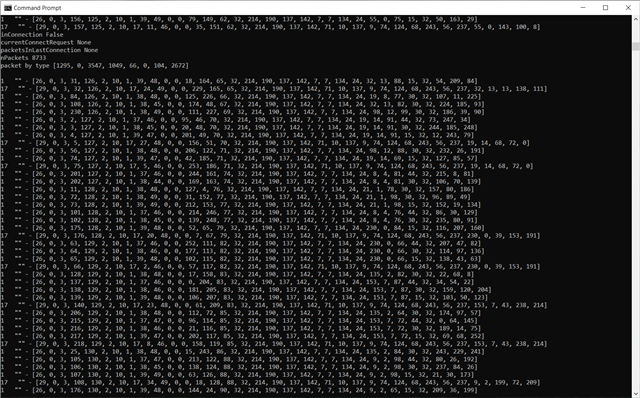
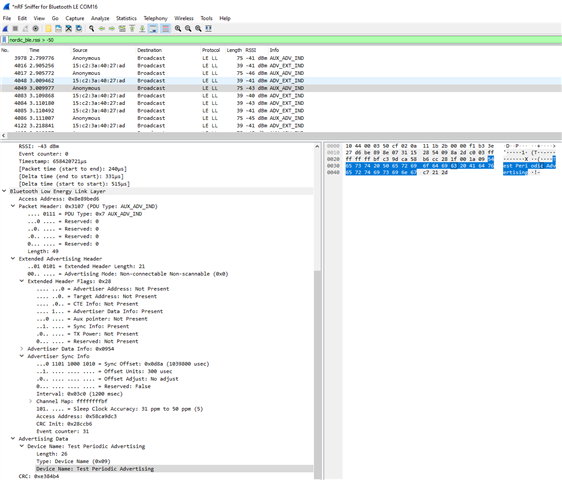
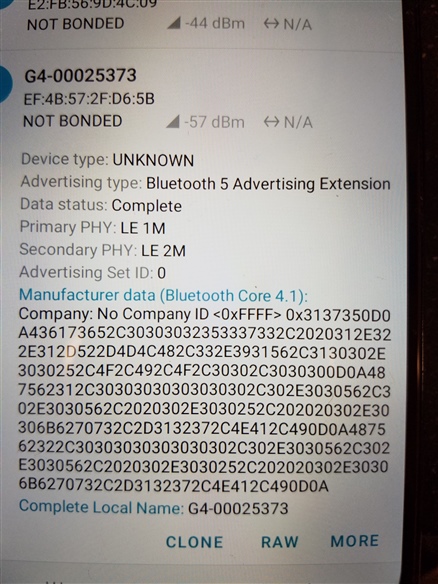
I connect to the nRF52840-MDK dongle thru the Serial Terminal (nRF52 Connectivity) it found the comm port and set the baudrate automatically. However, the terminal window constantly fills up the screen with ~/ characters. it repeats every 1 second. What I would like is detailed instructions on how to configure this dongle to be a BT 5 sniffer and read the Extended Advertising for any BT device near the dongle. It would also be helpful to filter the devices seen. Eventually I like to use Python to filter the choices and obtain the advertises data where I can parse the data received. I'm using Windows 10 pro.
Thanks.