Hi,
Background Information:
-
Our product, BLE near-infrared device, is undergoing CRA (Cyber Resilience Act) compliance assessment—specifically for the EU RED Cybersecurity Standard.
-
OpenCVE is a platform providing CVE data, focusing on security vulnerabilities across vendors and products.
-
Relevant link:
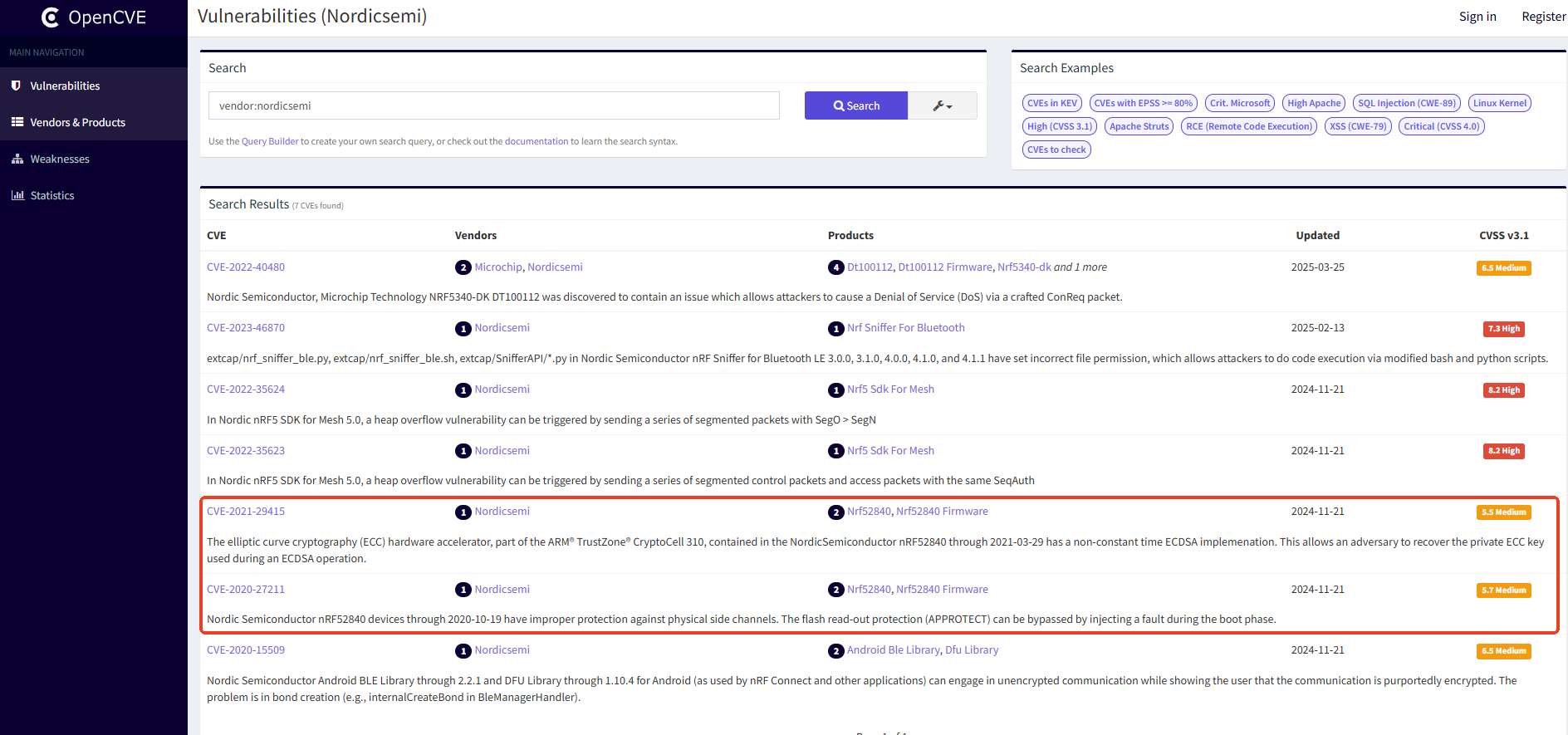
https://app.opencve.io/cve/?vendor=nordicsemi
-
Question:
Regarding the following two vulnerabilities, have they been resolved? If yes, is there supporting evidence?
-
CVE-2021-29415
The elliptic curve cryptography (ECC) hardware accelerator, part of the ARM
TrustZone
CryptoCell 310, contained in the Nordic Semiconductor nRF52840 through 2021-03-29 has a non-constant time ECDSA implementation. This allows an adversary to recover the private ECC key used during an ECDSA operation.
-
CVE-2020-27211
Nordic Semiconductor nRF52840 devices through 2020-10-19 have improper protection against physical side channels. The flash read-out protection (APPROTECT) can be bypassed by injecting a fault during the boot phase.


