Hi everyone,
I am facing an issue when modifying the peripheral_nfc_pairing example.
Due to hardware limitations, my device cannot integrate an NFC antenna. Instead, I plan to use an external NFC tag attached to the device. When a phone (Central) taps the NFC tag, it should trigger the pairing process.
My idea is to fix some parameters (e.g., TK) in the OOB record and write them into the NFC tag. The goal is to achieve Legacy OOB Pairing with Security Level 3.
Currently, I am testing on an nRF5340 DK with NFC antenna (not yet using an external NFC tag), running nRF Connect SDK 2.9.1.
However, after applying my modifications, the pairing only results in Security Level 2.
My modifications:
-
I use a fixed
tk_valueinstead of generating random TK. -
Replaced all usage of
tk_valuewithtk_value_fixed, including in the record payload.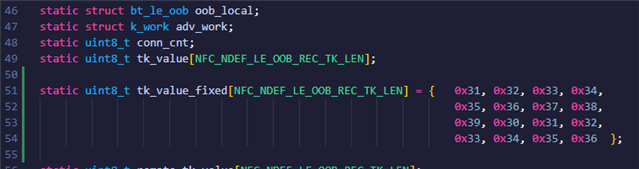
-
In the OOB record payload, I did not provide
le_sc_data, to enforce Legacy Pairing.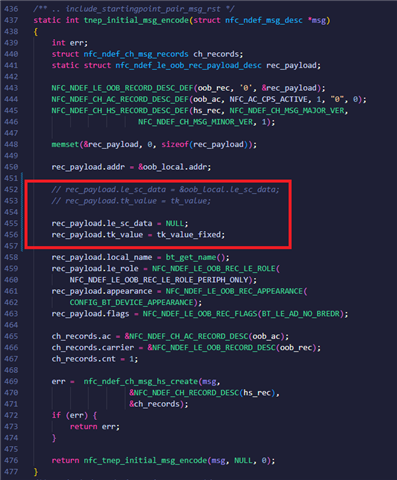
Observed results:
-
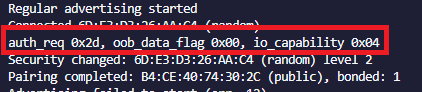
The connection only achieves Security Level 2, and it seems the OOB data is not used.
-
In the
pairing_acceptcallback, the SC flag inauth_reqis still set, andoob_data_flag= 0.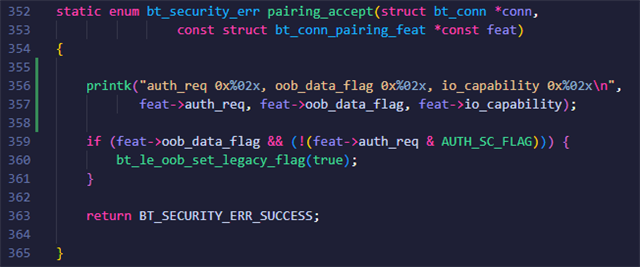
-
The
auth_oob_requestcallback is never called.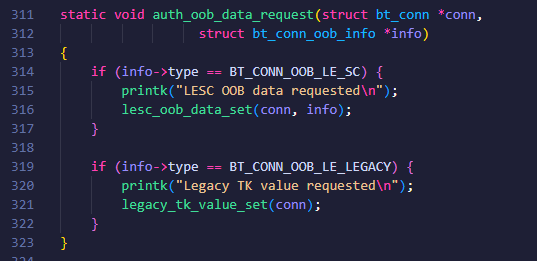
Questions:
-
Am I misunderstanding the OOB mechanism, or am I going in the wrong direction?
-
Is the idea of using an NFC tag with fixed TK for Legacy OOB Pairing feasible?
Any ideas or suggestions would be greatly appreciated.
Thank you very much!


