We want to measure latency and PER between two OpenThread Nodes exposed to WiFi interference.
Multiple Raspberry PIs, which are configured as AP and/or client, simulate flooded WiFi Traffic with iperf3.
Two NRF54L15 are used to build an OpenThread link (CONFIG_OPENTHREAD=y, CONFIG_OPENTHREAD_NORDIC_LIBRARY_MASTER=n) in the same frequency band as the WiFi.
A simple ID is exchanged between the nodes (otIcmp6SendEchoRequest) to calculate the roundtrip time and the PER. A delay of 250ms between two messages is added.
The two nodes are synced with CONFIG_OPENTHREAD_TIME_SYNC.
The Rapsberry PIs are physically arranged as a rectangle, with the two NRF54L15 in the middle.
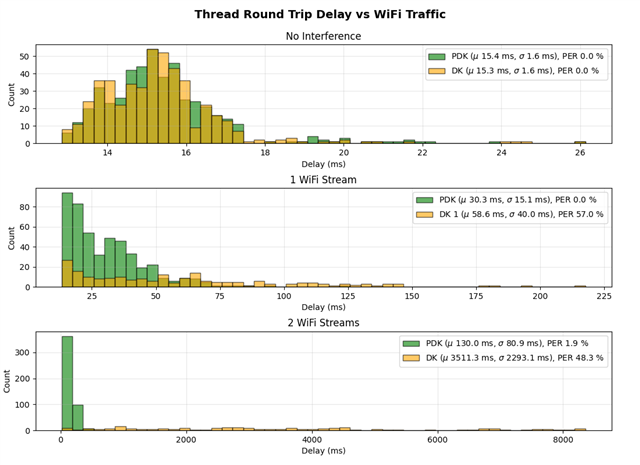
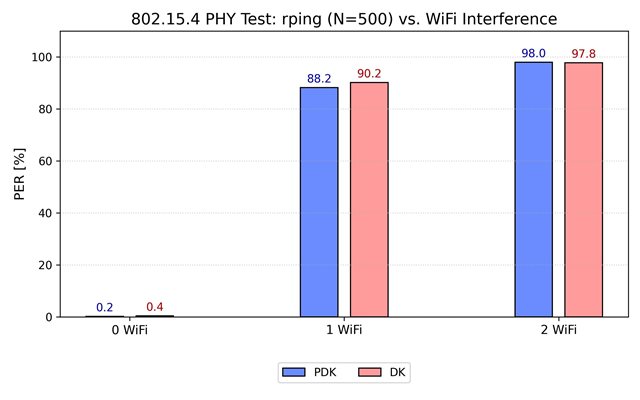
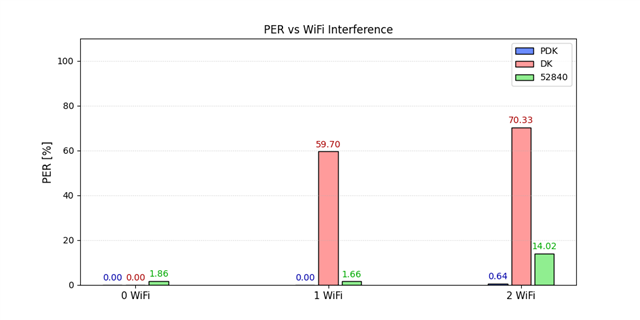
Measurements with the NRF54L15PDK yield the expected results (More interference results in higher Roundtriptime/PER).
However, if we use the same code/same build config with the NRF54L15DK, the ping sender crashes (Secure Fault) under heavy WiFi Interference.
Resistance to interference also appears to be lower, as indicated by a much higher PER for the DK compared to the PDK.
We checked with 4 different NRF54L15DK and tried different message sizes (64/127 bytes) for the ping.
Nothing is listed in the errata for the two different DKs and the specific SoC Version respectively.
How can the same code, yield two completely different results?
Are there some changes, which are not listed in the errata or in other words: What could be the issue for this behaviour?
Any help is appreciated.
Kind regards
Used Versions:
nRF Connect SDK v3.1.1 (Zephyr 4.1.99, west 1.4.0), Build config: nrf54l15dk/nrf54l15/cpuapp/ns
OpenThread: v 1.4
NRF54L15DK: v1.0.0 (SoC Ref 2)
NRF54L15PDK: v0.8.1 (SoC Ref 1)