Hi,
I am implementing a custom bootloader on an nRF52840. The firmware update is downloaded while the main application is running. The flow is as follows:
-
The application receives update information over MQTT (version, firmware size, hash, signature, and URL).
-
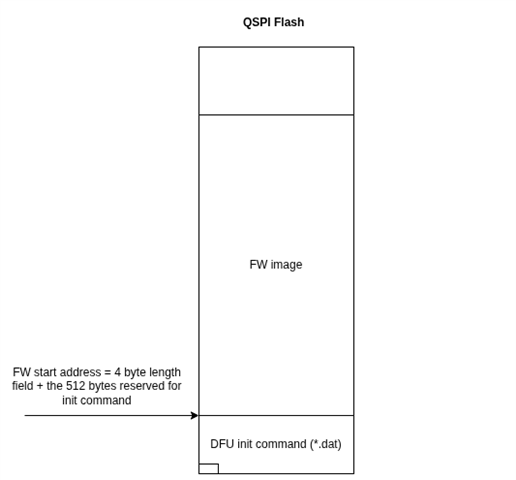
The application downloads the new firmware from the given URL into external flash.
-
The metadata (hash + signature + version info) is stored in the bootloader settings area.
-
The device is reset.
-
On startup, the bootloader checks if new firmware exists in the external flash region.
-
The bootloader calculates the hash of the firmware and compares it with the stored hash.
-
If the hash matches, the bootloader attempts to verify the signature using
nrf_crypto_ecdsa_verify().
Issue:
The call to nrf_crypto_ecdsa_verify() always fails. I am using curve SECP256R1.
I have tried:
-
Swapping public key and signature endianness (both LE and BE).
-
Splitting the signature and key into two 32-byte components and swapping individually.
-
Confirming the hash is correct. (Comparing the saved and calculated hash succeeds)
To validate the correctness of hash, signature, and public key, I wrote a Python script using cryptography.hazmat.primitives.asymmetric.ec with SECP256R1, and there the verification succeeds. So the signature and data are correct.
Questions:
-
Does
nrf_crypto_ecdsa_verifyexpect the hash, signature, and key in raw big-endian or little-endian format? -
For the public key, should it be passed as a concatenated buffer
[X || Y]or in some other internal representation? -
For the signature, should it be provided as raw 64 bytes
(r || s), or DER encoded?