We are using nRF54L15 devices and have enabled secure boot.
Our current setup is:
-
Firmware images are signed with a private key
-
The corresponding public key is provisioned into the device (via KMU)
-
Unsigned firmware is rejected during FOTA, and rollback works as expected
This provides protection against unauthorized FOTA updates.
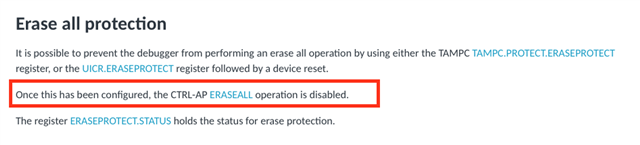
However, we observe that using ERASEALL or the nrfutil device recover command erases the KMU contents, including the provisioned public key. After recovery, the device can be flashed with a new firmware image, which will then run.
-
We want to store the public key in one-time programmable (OTP / eFuse) memory
-
Once provisioned, the key must not be erasable, changeable, or replaceable, even after ERASEALL or recovery
-
Only firmware correctly signed with the corresponding private key should ever boot
-
If verification fails, the device should remain locked / unusable
Is there any such facility available in the NRF54L15 device along with NRF SDK