nrf5340
NCS 3.1.0
Hello,
I am trying to improve boot time and here are some spikes and timings.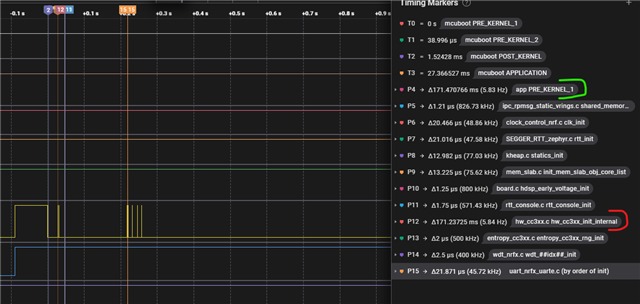
What I have found out is that CryptoCell init (hw_cc3xx_init_internal) takes majority of PRE_KERNEL_1 time.
As Crypto is not used early in the application, idea was to defer init of the driver, but I didn't had any success.
I've tried to comment out both SYS_INIT for hw_cc3xx_init (with and witout mutex), commented out entropy_cc3xx_rng_init, commented out _psa_crypto_init SYS_INIT and called those functions from main().
This is not working, board keeps rebooting
just for a test:
* I've tried to disable completely CC312 hardware and use Oberon instead without success.
* I've also tried to set zephyr,deferred-init; for &cryptocell. This just makes device disabled, but that 171ms function is still called in PRE_KERNEL_1
Do you have any recommendation how to make CryptoCell driver initialization later, during application run?
Thank you in advance,
Nemanja


