- nRF connection Desktop v5.2.0
- Toolchain Manager v1.6.0
- Visual studio cade v2.9.2
- Windows 11 pro Platform
Hi,
What access point are you using? It could be that the access point does not support TWT.
Can you share device logs when enabling TWT? You can also try the Wi-Fi TWT sample.
Best regards,
Marte
Hi,
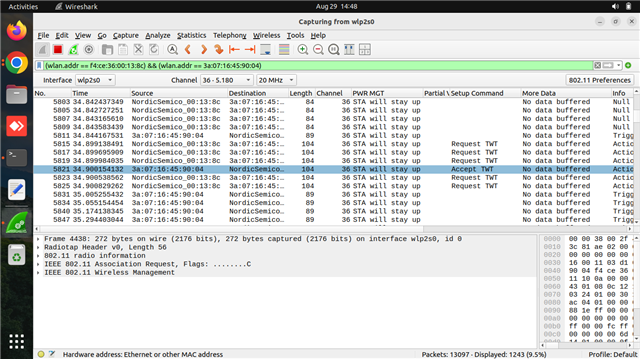
We are currently using a FreeBox Access Point, which supports TWT (Target Wake Time) power save mode. In the packet capture, we can see both the TWT Request and Accept frames. However, the client is still not entering power save mode.
TWT enabling logs:-
uart:~$ wifi twt setup 0 0 2 2 0 1 1 1 2000 60000
TWT operation TWT setup with dg: 2, flow_id: 2 requested
TWT response: TWT accept
== TWT negotiated parameters ==
TWT Dialog token: 2
TWT flow ID: 1
TWT negotiation type: TWT individual negotiation
TWT responder: true
TWT implicit: true
TWT announce: true
TWT trigger: true
TWT wake interval: 2048 us
TWT interval: 60000 us
For your reference Pcap screenshot attached below.
Thanks & regards,
Naveen P
Hi Naveen
Naveen Pyda said:We also added the credentials in prj.conf, but the client is not connecting to the SSID.
Did you set the credentials by changing these configs to the SSID and password for your network?
CONFIG_WIFI_CREDENTIALS_STATIC_SSID="MySSID" CONFIG_WIFI_CREDENTIALS_STATIC_PASSWORD="MyPassword"
What kind of security does the network use? In prj.conf, in the sample I shared, I set CONFIG_WIFI_CREDENTIALS_STATIC_TYPE_PSK, which is used if a network uses a password and PSK security, which is the most standard. If your network uses something else, you need to change this config to match your network's configuration. Here you can see the different config options for this:
Naveen Pyda said:Could you please guide us on how to run the TWT setup command:wifi twt setup 0 0 2 2 0 1 1 1 2000 60000000?
You do not need to run this command in the sample I shared, as the sample sets up TWT in the code itself:
static int setup_twt(void)
{
struct net_if *iface = net_if_get_first_wifi();
struct wifi_twt_params params = { 0 };
int ret;
twt_flow_id = 1;
params.operation = WIFI_TWT_SETUP;
params.negotiation_type = WIFI_TWT_INDIVIDUAL;
params.setup_cmd = WIFI_TWT_SETUP_CMD_REQUEST;
params.dialog_token = 1;
params.flow_id = twt_flow_id;
params.setup.responder = 0;
params.setup.trigger = IS_ENABLED(CONFIG_TWT_TRIGGER_ENABLE);
params.setup.implicit = 1;
params.setup.announce = IS_ENABLED(CONFIG_TWT_ANNOUNCED_MODE);
params.setup.twt_wake_interval = CONFIG_TWT_WAKE_INTERVAL;
params.setup.twt_interval = CONFIG_TWT_INTERVAL;
ret = net_mgmt(NET_REQUEST_WIFI_TWT, iface, ¶ms, sizeof(params));
if (ret) {
LOG_INF("TWT setup failed: %d", ret);
return ret;
}
LOG_INF("TWT setup requested");
return 0;
}
When the device connects to the network, it will send a request to enable TWT on its own.
Best regards,
Marte
Hi Marte,
Did you set the credentials by changing these configs to the SSID and password for your network?
Fullscreen12CONFIG_WIFI_CREDENTIALS_STATIC_SSID="MySSID"CONFIG_WIFI_CREDENTIALS_STATIC_PASSWORD="MyPassword"XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXCONFIG_WIFI_CREDENTIALS_STATIC_SSID="MySSID" CONFIG_WIFI_CREDENTIALS_STATIC_PASSWORD="MyPassword"What kind of security does the network use? In prj.conf, in the sample I shared, I set
Now the client is connected to the SSID and working as expected, but we want to run ping traffic on this client.
Please find the attached logs below for your reference:
*** Booting nRF Connect SDK v2.9.2-4ab7b98fc76f ***
*** Using Zephyr OS v3.7.99-aa34a5632971 ***
[00:00:00.486,999] <inf> net_config: Initializing network
[00:00:00.486,999] <inf> net_config: Waiting interface 1 (0x20001080) to be up...
[00:00:00.487,182] <inf> net_config: IPv4 address: 192.168.1.99
[00:00:00.487,213] <inf> net_config: Running dhcpv4 client...
[00:00:00.487,457] <inf> twt: Starting nrf7002dk with CPU frequency: 64 MHz
[00:00:00.489,349] <inf> wifi_supplicant: wpa_supplicant initialized
[00:00:01.487,579] <inf> twt: Static IP address (overridable): 192.168.1.99/255.255.255.0 -> 192.168.1.1
[00:00:03.419,860] <inf> wifi_mgmt_ext: Connection requested
[00:00:03.419,891] <inf> twt: Connection requested
[00:00:03.419,952] <inf> twt: ==================
[00:00:03.419,982] <inf> twt: State: SCANNING
[00:00:03.720,123] <inf> twt: ==================
[00:00:03.720,153] <inf> twt: State: SCANNING
[00:00:04.020,324] <inf> twt: ==================
[00:00:04.020,355] <inf> twt: State: SCANNING
[00:00:04.320,495] <inf> twt: ==================
[00:00:04.320,495] <inf> twt: State: SCANNING
[00:00:04.620,666] <inf> twt: ==================
[00:00:07.322,296] <inf> twt: State: AUTHENTICATING
[00:00:07.622,436] <inf> twt: ==================
[00:00:07.622,467] <inf> twt: State: AUTHENTICATING
[00:00:07.940,948] <inf> twt: ==================
[00:00:07.940,979] <inf> twt: State: ASSOCIATED
[00:00:07.941,009] <inf> twt: Interface Mode: STATION
[00:00:07.941,009] <inf> twt: Link Mode: WIFI 6 (802.11ax/HE)
[00:00:07.941,040] <inf> twt: SSID: TWT
[00:00:07.941,070] <inf> twt: BSSID: 00:33:58:AB:81:82
[00:00:07.941,101] <inf> twt: Band: 5GHz
[00:00:07.941,101] <inf> twt: Channel: 64
[00:00:07.941,131] <inf> twt: Security: WPA2-PSK
[00:00:07.941,131] <inf> twt: MFP: Optional
[00:00:07.941,162] <inf> twt: RSSI: -56
[00:00:07.941,162] <inf> twt: TWT: Supported
[00:00:07.994,842] <inf> twt: Connected
[00:00:08.248,474] <inf> twt: ==================
[00:00:08.248,504] <inf> twt: State: COMPLETED
[00:00:08.248,535] <inf> twt: Interface Mode: STATION
[00:00:08.248,565] <inf> twt: Link Mode: WIFI 6 (802.11ax/HE)
[00:00:08.248,596] <inf> twt: SSID: TWT
[00:00:08.248,626] <inf> twt: BSSID: 00:33:58:AB:81:82
[00:00:08.248,626] <inf> twt: Band: 5GHz
[00:00:08.248,657] <inf> twt: Channel: 64
[00:00:08.248,657] <inf> twt: Security: WPA2-PSK
[00:00:08.248,687] <inf> twt: MFP: Optional
[00:00:08.248,687] <inf> twt: RSSI: -55
[00:00:08.248,718] <inf> twt: TWT: Supported
[00:00:09.273,620] <inf> net_dhcpv4: Received: 172.40.9.251
[00:00:09.273,803] <inf> net_config: IPv4 address: 172.40.9.251
[00:00:09.273,803] <inf> net_config: Lease time: 600 seconds
[00:00:09.273,864] <inf> net_config: Subnet: 255.255.240.0
[00:00:09.273,895] <inf> net_config: Router: 172.40.0.1
[00:00:09.273,986] <inf> twt: DHCP IP address: 172.40.9.251
[00:00:10.248,779] <inf> twt: AP is TWT capable, establishing TWT
[00:00:10.256,622] <inf> twt: TWT setup requested
[00:00:10.282,958] <inf> twt: TWT response: TWT accept
[00:00:10.282,958] <inf> twt: == TWT negotiated parameters ==
[00:00:10.282,989] <inf> twt: TWT Dialog token: 1
[00:00:10.282,989] <inf> twt: TWT flow ID: 1
[00:00:10.283,020] <inf> twt: TWT negotiation type: TWT individual negotiation
[00:00:10.283,020] <inf> twt: TWT responder: true
[00:00:10.283,050] <inf> twt: TWT implicit: true
[00:00:10.283,081] <inf> twt: TWT announce: false
[00:00:10.283,111] <inf> twt: TWT trigger: false
[00:00:10.283,111] <inf> twt: TWT wake interval: 65024 us
[00:00:10.283,111] <inf> twt: TWT interval: 524000 us
[00:00:10.283,111] <inf> twt: ========================
[00:00:10.283,264] <inf> twt: TWT sleep state: sleeping
[00:00:10.412,811] <inf> twt: TWT sleep state: awake
[00:00:10.477,783] <inf> twt: TWT sleep state: sleeping
[00:00:10.556,701] <inf> twt: TWT Setup success
[00:00:10.937,164] <inf> twt: TWT sleep state: awake
[00:00:11.002,258] <inf> twt: TWT sleep state: sleeping
[00:00:11.461,486] <inf> twt: TWT sleep state: awake
[00:00:11.526,672] <inf> twt: TWT sleep state: sleeping
[00:00:11.985,809] <inf> twt: TWT sleep state: awake
[00:00:12.051,086] <inf> twt: TWT sleep state: sleeping
Thanks & Regards,
Naveen P
Hi Marte,
we want to run ping traffic on this client.
And we want to run iperf or zperf.
Hi Marte,
Any updates on this?
Hi,
Based on the logs with the TWT sample, the device enters sleep mode as it should, so this is most likely also the case when you use the shell sample. In other words, you can chose to use the TWT sample I shared or the Wi-Fi shell sample in the SDK for TWT.
If you want to use the TWT sample I shared, you can enable zperf by adding the following in prj.conf:
CONFIG_NET_SHELL=y CONFIG_NET_ZPERF=y CONFIG_ZVFS_OPEN_MAX=12
This lets you use iperf/zperf as in the Wi-Fi Throughput sample, i.e., you can use the following command on the nRF7002:
zperf udp upload <ipaddress> 5001 10 1K 50M zperf udp download 5001
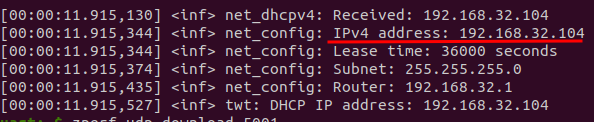
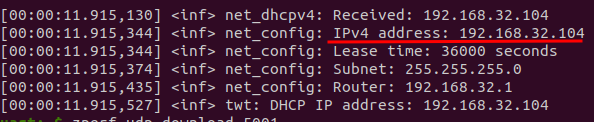
If you get any errors, you might have to increase CONFIG_ZVFS_OPEN_MAX and CONFIG_NET_SOCKETS_POLL_MAX. You should also remove CONFIG_NET_CONFIG_MY_IPV4_ADDR from prj.conf, as if you have this, zperf will try to use the address set there instead of the device's actual address. You can see the device's address in the log:
Best regards,
Marte
Hi,
Based on the logs with the TWT sample, the device enters sleep mode as it should, so this is most likely also the case when you use the shell sample. In other words, you can chose to use the TWT sample I shared or the Wi-Fi shell sample in the SDK for TWT.
If you want to use the TWT sample I shared, you can enable zperf by adding the following in prj.conf:
CONFIG_NET_SHELL=y CONFIG_NET_ZPERF=y CONFIG_ZVFS_OPEN_MAX=12
This lets you use iperf/zperf as in the Wi-Fi Throughput sample, i.e., you can use the following command on the nRF7002:
zperf udp upload <ipaddress> 5001 10 1K 50M zperf udp download 5001
If you get any errors, you might have to increase CONFIG_ZVFS_OPEN_MAX and CONFIG_NET_SOCKETS_POLL_MAX. You should also remove CONFIG_NET_CONFIG_MY_IPV4_ADDR from prj.conf, as if you have this, zperf will try to use the address set there instead of the device's actual address. You can see the device's address in the log:
Best regards,
Marte
Hi Marte,
As you mentioned, we are getting logs in the TWT sample. However, in the Pcap capture, we are not able to see the client entering sleep mode. For your reference, I have attached the Pcap files
If you want to use the TWT sample I shared, you can enable zperf by adding the following in prj.conf:
Fullscreen123CONFIG_NET_SHELL=yCONFIG_NET_ZPERF=yCONFIG_ZVFS_OPEN_MAX=12XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXCONFIG_NET_SHELL=y CONFIG_NET_ZPERF=y CONFIG_ZVFS_OPEN_MAX=12
As per your suggestion, I added the three lines to the prj.conf file in the TWT sample. However, after making these changes, I encountered a new issue. Kindly find the logs below for your reference.
Please share the complete file with include these three lines.
Logs :-
:00:00.346,221] <inf> wifi_nrf: Management buffer offload enabled
*** Booting nRF Connect SDK v2.9.2-4ab7b98fc76f ***
*** Using Zephyr OS v3.7.99-aa34a5632971 ***
[00:00:00.475,280] <inf> net_config: Initializing network
[00:00:00.475,280] <inf> net_config: Waiting interface 1 (0x20001300) to be up...
[00:00:00.475,463] <inf> net_config: IPv4 address: 192.168.1.99
[00:00:00.475,494] <inf> net_config: Running dhcpv4 client...
[00:00:00.475,738] <inf> twt: Starting nrf7002dk with CPU frequency: 64 MHz
[00:00:00.477,386] <inf> wifi_supplicant: wpa_supplicant initialized
[00:00:00.512,420] <err> wifi_supplicant: Failed to initialize supplicant control interface
[00:00:01.475,860] <inf> twt: Static IP address (overridable): 192.168.1.99/255.255.255.0 -> 192.168.1.1
[00:00:01.475,982] <err> wifi_mgmt_ext: Connection request failed
[00:00:01.475,982] <err> twt: Connection request failed
[00:00:01.476,013] <inf> twt: Status request failed: -134
[00:00:01.776,092] <inf> twt: Status request failed: -134
[00:00:02.076,202] <inf> twt: Status request failed: -134
[00:00:02.376,312] <inf> twt: Status request failed: -134
[00:00:02.676,483] <inf> twt: Status request failed: -134
[00:00:02.976,593] <inf> twt: Status request failed: -134
[00:00:03.276,702] <inf> twt: Status request failed: -134
[00:00:03.576,812] <inf> twt: Status request failed: -134
[00:00:03.876,983] <inf> twt: Status request failed: -134
[00:00:04.177,062] <inf> twt: Status request failed: -134
[00:00:04.477,233] <inf> twt: Status request failed: -134
[00:00:04.777,313] <inf> twt: Status request failed: -134
[00:00:05.077,484] <inf> twt: Status request failed: -134
[00:00:05.377,593] <inf> twt: Status request failed: -134
[00:00:05.677,703] <inf> twt: Status request failed: -134
[00:00:05.977,813] <inf> twt: Status request failed: -134
[00:00:06.277,984] <inf> twt: Status request failed: -134
[00:00:06.578,094] <inf> twt: Status request failed: -134
[00:00:06.878,204] <inf> twt: Status request failed: -134
[00:00:07.178,314] <inf> twt: Status request failed: -134
[00:00:07.478,485] <inf> twt: Status request failed: -134
[00:00:07.778,594] <inf> twt: Status request failed: -134
[00:00:08.078,704] <inf> twt: Status request failed: -134
[00:00:08.378,814] <inf> twt: Status request failed: -134
https://drive.google.com/file/d/14Fs-UamPPC6dTh4ZYP61TrN7U21sawLM/view?usp=drive_link
Thanks & Regards,
Naveen P
Hi Merte,
Any update on this, please?
Hi Merte,
Any update on this, please?
Hi,
Did you also follow:
Marte Myrvold said:If you get any errors, you might have to increase CONFIG_ZVFS_OPEN_MAX and CONFIG_NET_SOCKETS_POLL_MAX. You should also remove CONFIG_NET_CONFIG_MY_IPV4_ADDR from prj.conf, as if you have this, zperf will try to use the address set there instead of the device's actual address. You can see the device's address in the log:
Kenneth