Hello DevZone,
I have a confusing question about TF-M. Need help from a TF-M expert.
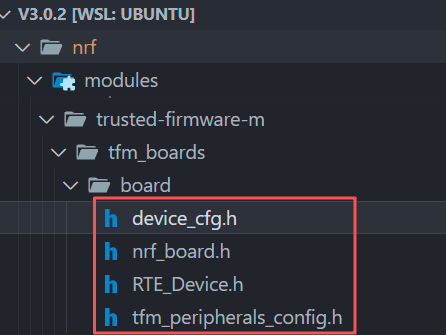
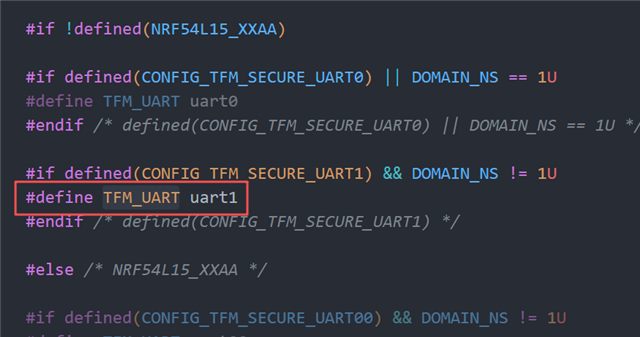
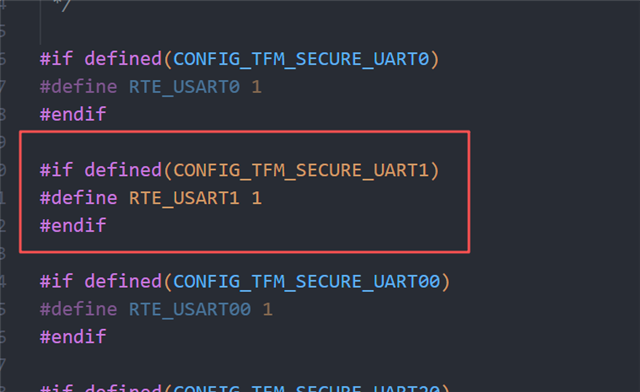
In this document, it says that we must disable uart1 in non-secure application, because TF-M use it as secure peripheral.
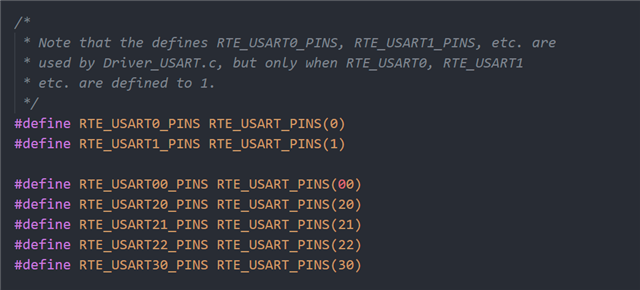
My question is: how does TF-M select the pins used by uart1_secure?
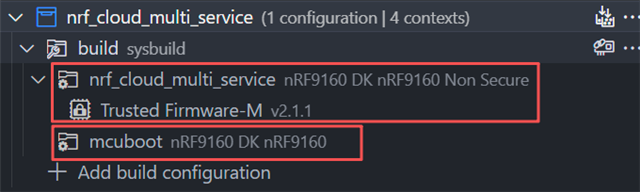
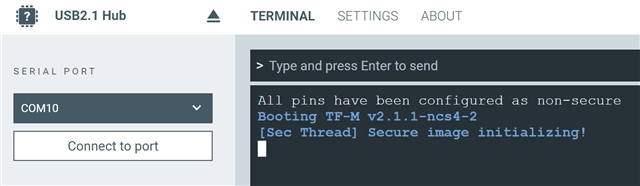
My board selection is `nrf9160dk/nrf9160/ns`, which is a non-secure board.
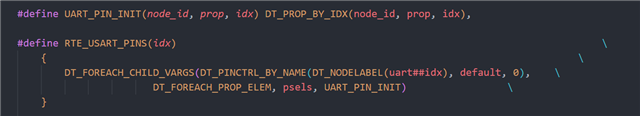
I use AI to read the build progress and all the Ninja things. And it told me that TF-M just read the non-secure `zephyr.dts` and use the pin-ctrl of that.
I think this is not reasonable, because uart1 is disabled in my application. There is no reason for TF-M to use the pin-ctrl from a disabled uart.
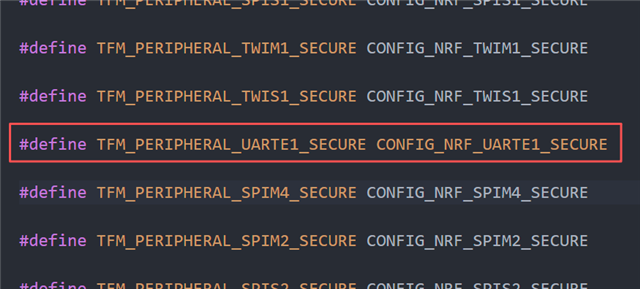
More general question: how can I choose a peripheral as secure or non-secure in NCS? Should I configure this in Devicetree or Kconfig?
Best regards,
Jayant