I have followed the guide to do a serial recovery of the appcore and it's working fine. Now I would like to be able to update both the appcore and the netcore.
I have configured my project as follow:
sysbuild.conf
SB_CONFIG_BOOTLOADER_MCUBOOT=y # use hci ipc as netcore child image SB_CONFIG_NETCORE_HCI_IPC=y # use netcore bootloader as child image # secure bootloader is required for netcore bootloader see: # https://docs.nordicsemi.com/bundle/ncs-latest/page/nrf/samples/nrf5340/netboot/README.html#building_and_running SB_CONFIG_SECURE_BOOT_NETCORE=y # secure boot on appcore doesn't seem to be required SB_CONFIG_SECURE_BOOT_APPCORE=n # required to update netcore image from appcore using mcuboot SB_CONFIG_NETCORE_APP_UPDATE=y # one image pair mode without scratch partition SB_CONFIG_MCUBOOT_NRF53_MULTI_IMAGE_UPDATE=n SB_CONFIG_MCUBOOT_UPDATEABLE_IMAGES=1 SB_CONFIG_MCUBOOT_MODE_SINGLE_APP=y # Match MCUboot signing type with keys/appcore_debug_mcuboot_private.pem (EC P-256) SB_CONFIG_BOOT_SIGNATURE_TYPE_ECDSA_P256=y
mcuboot.conf
CONFIG_FLASH=y # serial recovery CONFIG_MCUBOOT_SERIAL=y CONFIG_BOOT_SERIAL_UART=y CONFIG_BOOT_SERIAL_ENTRANCE_GPIO=n CONFIG_BOOT_SERIAL_WAIT_FOR_DFU=y CONFIG_BOOT_SERIAL_WAIT_FOR_DFU_TIMEOUT=500 CONFIG_BOOT_SERIAL_NO_APPLICATION=y CONFIG_BOOT_SERIAL_BOOT_MODE=y # boot mode retention CONFIG_RETENTION=y CONFIG_RETAINED_MEM=y CONFIG_RETAINED_MEM_ZEPHYR_RAM=y CONFIG_RETENTION_BOOT_MODE=y # serial recovery netcore CONFIG_BOOT_IMAGE_ACCESS_HOOKS=y CONFIG_FLASH_SIMULATOR=y CONFIG_FLASH_SIMULATOR_DOUBLE_WRITES=y CONFIG_FLASH_SIMULATOR_STATS=n CONFIG_MCUBOOT_SERIAL_DIRECT_IMAGE_UPLOAD=y CONFIG_NRF53_RECOVERY_NETWORK_CORE=y CONFIG_PCD_APP=y # Decrease memory footprint CONFIG_SIZE_OPTIMIZATIONS=y CONFIG_CBPRINTF_NANO=y CONFIG_TIMESLICING=n CONFIG_BOOT_BANNER=n CONFIG_CONSOLE=n CONFIG_CONSOLE_HANDLER=n CONFIG_UART_CONSOLE=n CONFIG_USE_SEGGER_RTT=n CONFIG_LOG=n CONFIG_ERRNO=n CONFIG_PRINTK=n
prj.conf
CONFIG_MPSL_PIN_DEBUG=y # Some command handlers require a large stack. CONFIG_SYSTEM_WORKQUEUE_STACK_SIZE=4096 CONFIG_MAIN_STACK_SIZE=4096 # Current implementation of UART uses k_malloc and # therefore, heap must be >0 ... CONFIG_HEAP_MEM_POOL_SIZE=4096 # Required by the `taskstat` command. CONFIG_THREAD_MONITOR=y CONFIG_THREAD_NAME=y # Enable statistics and statistic names. CONFIG_STATS=y CONFIG_STATS_NAMES=y # Assert CONFIG_ASSERT=y CONFIG_HW_STACK_PROTECTION=y # Bluetooth config CONFIG_BT=y CONFIG_BT_HCI_RAW=y CONFIG_BT_HCI_RAW_H4=y CONFIG_BT_HCI_RAW_H4_ENABLE=y CONFIG_BT_BUF_ACL_TX_COUNT=8 CONFIG_BT_BUF_ACL_TX_SIZE=256 CONFIG_BT_BUF_ACL_RX_COUNT=8 CONFIG_BT_BUF_ACL_RX_SIZE=256 CONFIG_BT_ISO_BROADCASTER=y CONFIG_BT_ISO_CENTRAL=y CONFIG_BT_ISO_MAX_CHAN=2 # IPC CONFIG_IPC_SERVICE=y CONFIG_IPC_SERVICE_BACKEND_RPMSG=y # Audio codec LC3 related defines # FPU_SHARING enables preservation of the hardware floating point registers # across context switches to allow multiple threads to perform concurrent # floating point operations. CONFIG_FPU=y CONFIG_FPU_SHARING=y # NOTE: Since we are not using minimal libc, error codes from # minimal libc are not used CONFIG_NEWLIB_LIBC=y # I2S CONFIG_NRFX_I2S0=y # Enable the data first-in first-out library CONFIG_DATA_FIFO=y # Library for manipulating pulse coded modulation (PCM) streams CONFIG_PSCM=y # Configure UART async correctly CONFIG_SERIAL=y CONFIG_UART_ASYNC_API=y CONFIG_UART_INTERRUPT_DRIVEN=y CONFIG_UART_0_INTERRUPT_DRIVEN=n CONFIG_UART_1_INTERRUPT_DRIVEN=n CONFIG_UART_0_ASYNC=y CONFIG_UART_1_ASYNC=y CONFIG_NRFX_UARTE0=y CONFIG_NRFX_UARTE1=y CONFIG_UART_NRFX_UARTE_ENHANCED_RX=y CONFIG_UART_USE_RUNTIME_CONFIGURE=y # Audio sync timer CONFIG_NRFX_TIMER1=y # Boot mode CONFIG_RETENTION=y CONFIG_RETAINED_MEM=y CONFIG_RETAINED_MEM_ZEPHYR_RAM=y CONFIG_RETENTION_BOOT_MODE=y CONFIG_REBOOT=y # Enable PSA Crypto with hardware acceleration CONFIG_PSA_CRYPTO_DRIVER_CC3XX=y CONFIG_PSA_CRYPTO_DRIVER_OBERON=n # Enable CryptoCell CC312 hardware CONFIG_HW_CC3XX=y CONFIG_CC3XX_BACKEND=y # Enable nordic security backend and PSA APIs CONFIG_NRF_SECURITY=y CONFIG_MBEDTLS_PSA_CRYPTO_C=y CONFIG_PSA_WANT_ALG_ECDH=y CONFIG_PSA_WANT_KEY_TYPE_ECC_KEY_PAIR_GENERATE=y CONFIG_PSA_WANT_KEY_TYPE_ECC_KEY_PAIR_IMPORT=y CONFIG_PSA_WANT_KEY_TYPE_ECC_KEY_PAIR_EXPORT=y CONFIG_PSA_WANT_ECC_SECP_R1_256=y CONFIG_PSA_WANT_KEY_TYPE_ECC_PUBLIC_KEY=y # For key generation CONFIG_PSA_WANT_GENERATE_RANDOM=y CONFIG_MBEDTLS_ENABLE_HEAP=y CONFIG_MBEDTLS_HEAP_SIZE=16384
I have a partition manager applied as follow:
flash_primary (0x100000 - 1024kB): +--------------------------------------------------+ +---0x0: b0_container (0x8000 - 32kB)--------------+ | 0x0: b0 (0x8000 - 32kB) | +---0x8000: s0 (0xc000 - 48kB)---------------------+ | 0x8000: s0_pad (0x200 - 512B) | +---0x8200: s0_image (0xbe00 - 47kB)---------------+ | 0x8200: mcuboot (0xbe00 - 47kB) | +--------------------------------------------------+ | 0x14000: EMPTY_0 (0x4000 - 16kB) | +---0x18000: s1 (0xc000 - 48kB)--------------------+ | 0x18000: s1_pad (0x200 - 512B) | | 0x18200: s1_image (0xbe00 - 47kB) | +--------------------------------------------------+ | 0x24000: EMPTY_1 (0x4000 - 16kB) | +---0x28000: mcuboot_primary (0x6c000 - 432kB)-----+ | 0x28000: mcuboot_pad (0x200 - 512B) | +---0x28200: app_image (0x6be00 - 431kB)-----------+ +---0x28200: mcuboot_primary_app (0x6be00 - 431kB)-+ | 0x28200: app (0x6be00 - 431kB) | +--------------------------------------------------+ | 0x94000: mcuboot_secondary (0x6c000 - 432kB) | | 0xb8000: mcuboot_secondary_1 (0x40000 - 256kB) | | 0xf8000: settings_storage (0x8000 - 32kB) | +--------------------------------------------------+ otp (0x2fc - 764B): +------------------------------+ | 0xff8100: otp (0x2fc - 764B) | +------------------------------+ ram_flash (0x40000 - 256kB): +------------------------------------------+ | 0x0: mcuboot_primary_1 (0x40000 - 256kB) | | 0x40000: ram_flash (0x0 - 0B) | +------------------------------------------+ sram_primary (0x3ffff - 255kB): +-----------------------------------------------+ | 0x20000000: pcd_sram (0x2000 - 8kB) | | 0x20002000: sram_retained_mem (0x400 - 1kB) | | 0x20002400: sram_primary (0x2dbff - 182kB) | | 0x2002ffff: rpmsg_nrf53_sram (0x10000 - 64kB) | +-----------------------------------------------+ CPUNET flash_primary (0x40000 - 256kB): +--------------------------------------------+ +---0x1000000: b0n_container (0x8800 - 34kB)-+ | 0x1000000: b0n (0x8580 - 33kB) | | 0x1008580: provision (0x280 - 640B) | +---0x1008800: app (0x37800 - 222kB)---------+ | 0x1008800: hci_ipc (0x37800 - 222kB) | +--------------------------------------------+ CPUNET sram_primary (0x10000 - 64kB): +-------------------------------------------+ | 0x21000000: sram_primary (0x10000 - 64kB) | +-------------------------------------------+
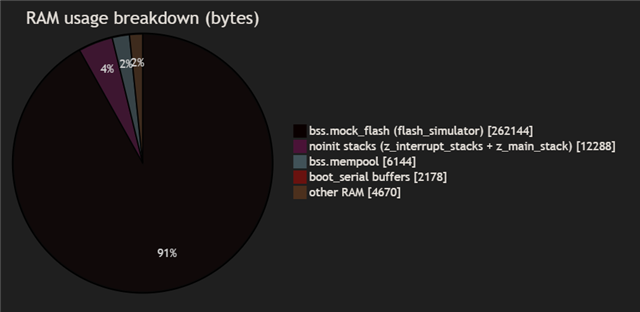
The problem is that the ram is overflowed by a lot due to the mock_flash partition:
-- Zephyr version: 4.1.99 (/workspace/_nordic_sdk/zephyr), build: ff8f0c579eeb [202/207] Linking C executable zephyr/zephyr_pre0.elf FAILED: zephyr/zephyr_pre0.elf zephyr/zephyr_pre0.map /workspace/_obj/app/baseband_nordic/sdk_3_1/mezza_nordic/mcuboot/zephyr/zephyr_pre0.map : && ccache /opt/ncs/toolchains/b2ecd2435d/opt/zephyr-sdk/arm-zephyr-eabi/bin/arm-zephyr-eabi-gcc -gdwarf-4 zephyr/CMakeFiles/zephyr_pre0.dir/misc/empty_file.c.obj -o zephyr/zephyr_pre0.elf zephyr/CMakeFiles/offsets.dir/./arch/arm/core/offsets/offsets.c.obj -T zephyr/linker_zephyr_pre0.cmd -Wl,-Map=/workspace/_obj/app/baseband_nordic/sdk_3_1/mezza_nordic/mcuboot/zephyr/zephyr_pre0.map -Wl,--whole-archive app/libapp.a zephyr/libzephyr.a zephyr/arch/common/libarch__common.a zephyr/arch/arch/arm/core/libarch__arm__core.a zephyr/arch/arch/arm/core/cortex_m/libarch__arm__core__cortex_m.a zephyr/arch/arch/arm/core/cortex_m/cmse/libarch__arm__core__cortex_m__cmse.a zephyr/arch/arch/arm/core/mpu/libarch__arm__core__mpu.a zephyr/lib/libc/picolibc/liblib__libc__picolibc.a zephyr/lib/libc/common/liblib__libc__common.a zephyr/soc/soc/nrf5340/libsoc__nordic.a zephyr/boards/boards/arm/mezza_nordic/lib..__..__modules__phc_boards__boards__sonova__mezza_nordic.a zephyr/subsys/retention/libsubsys__retention.a zephyr/drivers/clock_control/libdrivers__clock_control.a zephyr/drivers/flash/libdrivers__flash.a zephyr/drivers/gpio/libdrivers__gpio.a zephyr/drivers/pinctrl/libdrivers__pinctrl.a zephyr/drivers/regulator/libdrivers__regulator.a zephyr/drivers/retained_mem/libdrivers__retained_mem.a zephyr/drivers/serial/libdrivers__serial.a zephyr/drivers/timer/libdrivers__timer.a modules/nrf/lib/fprotect/lib..__nrf__lib__fprotect.a modules/nrf/subsys/pcd/lib..__nrf__subsys__pcd.a modules/nrf/modules/mcuboot/hooks/lib..__nrf__modules__mcuboot__hooks.a modules/nrf/drivers/hw_cc3xx/lib..__nrf__drivers__hw_cc3xx.a modules/mcuboot/boot/bootutil/zephyr/libmcuboot_util.a modules/hal_nordic/modules/hal_nordic/nrfx/libmodules__hal_nordic__nrfx.a modules/zcbor/libmodules__zcbor.a -Wl,--no-whole-archive zephyr/kernel/libkernel.a -L/workspace/_obj/app/baseband_nordic/sdk_3_1/mezza_nordic/mcuboot/zephyr zephyr/arch/common/libisr_tables.a -mcpu=cortex-m33 -mthumb -mabi=aapcs -mfp16-format=ieee -mtp=soft -fuse-ld=bfd -Wl,--gc-sections -Wl,--build-id=none -Wl,--sort-common=descending -Wl,--sort-section=alignment -Wl,-u,_OffsetAbsSyms -Wl,-u,_ConfigAbsSyms -nostdlib -static -Wl,-X -Wl,-N -Wl,--orphan-handling=warn -Wl,-no-pie -specs=picolibc.specs -DPICOLIBC_MINIMAL_PRINTF_SCANF /workspace/_nordic_sdk/nrfxlib/crypto/nrf_cc312_platform/lib/cortex-m33/soft-float/no-interrupts/libnrf_cc312_platform_0.9.19.a -L"/opt/ncs/toolchains/b2ecd2435d/opt/zephyr-sdk/arm-zephyr-eabi/bin/../lib/gcc/arm-zephyr-eabi/12.2.0/thumb/v8-m.main/nofp" -lc -lgcc && cd /workspace/_obj/app/baseband_nordic/sdk_3_1/mezza_nordic/mcuboot/zephyr && /opt/ncs/toolchains/b2ecd2435d/usr/local/bin/cmake -E true /opt/ncs/toolchains/b2ecd2435d/opt/zephyr-sdk/arm-zephyr-eabi/bin/../lib/gcc/arm-zephyr-eabi/12.2.0/../../../../arm-zephyr-eabi/bin/ld.bfd: zephyr/zephyr_pre0.elf section `bss' will not fit in region `RAM' /opt/ncs/toolchains/b2ecd2435d/opt/zephyr-sdk/arm-zephyr-eabi/bin/../lib/gcc/arm-zephyr-eabi/12.2.0/../../../../arm-zephyr-eabi/bin/ld.bfd: region `RAM' overflowed by 91745 bytes
I have followed these guides:
MCUboot’s serial recovery of the networking core image
nRF5340: Network core bootloader
Any idea what is wrong?
The AI suggest to reduce the size of the sim_flash to fit only the hci_ipc image and effectively some memory are spared:
/opt/ncs/toolchains/b2ecd2435d/opt/zephyr-sdk/arm-zephyr-eabi/bin/../lib/gcc/arm-zephyr-eabi/12.2.0/../../../../arm-zephyr-eabi/bin/ld.bfd: zephyr/zephyr_pre0.elf section `bss' will not fit in region `RAM' /opt/ncs/toolchains/b2ecd2435d/opt/zephyr-sdk/arm-zephyr-eabi/bin/../lib/gcc/arm-zephyr-eabi/12.2.0/../../../../arm-zephyr-eabi/bin/ld.bfd: region `RAM' overflowed by 58977 bytes


